Last Updated on March 2, 2022 by Alarm New England
Access control is necessary for protecting your business from unauthorized visitors. In addition to providing protection, access control systems bring a host of benefits to help you manage access to areas in your business. There are several main types of access control systems, and each works differently to authorize and control visitors’ and employees’ access to what they need.
Types of Access Control Systems for Your Needs
Access control systems must meet all security needs regarding allowing employees and visitors access to your commercial facility. Your ideal access control type is dependent on your property’s safety and security requirements, as well as the people you intend to involve in your business.
All access control systems create a record in the system’s database when someone uses an access card or other method to enter and exit the premises or access digital resources. The way the owner or system administrator assigns permissions and gives access to employees and other people differs depending on the system type.
Some access control systems are more restrictive while others are more lenient in granting permissions. Many systems are based on the principle of least privilege, which dictates that employees should have no more than the minimal permissions required to perform their job duties adequately.
These strict principles allow employees access to only the exact tools and resources they need for their position and nothing else. Consider the following options when choosing an access control system for your business.
Discretionary access control
With a discretionary access control (DAC) system, the company owner determines who can access a particular location. This system also manages access to digital files and other resources. When an employee tries to enter through a particular access point, whether a digital or physical location, the DAC system checks against the list of people who have access and grants it by comparing it to the scanned fingerprint, card, or another form of identification.
DAC has its advantages of being flexible and easy to use, but it requires the owner to manage access actively. It also gives complete access to only one user over all other permissions, which owners can abuse when the permissions provide access to other programs.
Mandatory access control
Also called managed access control, mandatory access control (MAC) is a highly secure access control system standard in companies where confidentiality is necessary. Company owners do not control who has access to classified information or a restricted location, but they can access the MAC system. A system administrator sets all permissions for door entry, which prevents the wrong people from changing permissions and accessing information they don’t have the authority to see.
Mandatory access control is most popular with confidential military data due to its restrictive characteristics. The system sorts everyone who will use the program and either grants or denies access based on the criteria set by the system administrator. That said, the downside with this system is that the system administrator must permit the changes to the access control settings.
Role-based access control
A fast, new system for managing access control in a business is role-based access control (RBAC). Company owners create job titles within the system and assign specific permissions to each job, giving new access more quickly and easily, especially when employees change positions. Users must confirm their role in the system to gain access.
RBAC ensures that those who do not have the proper knowledge cannot perform tasks that require more experience than they have. When an employee gets a promotion, company owners can change their RBAC system role rather than wasting time assigning specific permissions to them. This is incredibly convenient due to the limited amount of time required to alter physical entry permissions or give access to programs for certain company positions.
Rule-based access control
Customization among access control systems is essential in providing the flexibility you need to protect your property, employees, and guests. Rule-based access control adds another layer of specificity to access control. System administrators set rules that determine when and how employees access locations and resources.
Combining rule-based and role-based access control is common to add further access restrictions that narrow permissions down to specific details. While role-based access control allows certain types of employees access on account of their job, rule-based access control can define other conditions such as hours of access.
Attribute-based access control
Another popular and easy-to-use system, attribute-based access control (ABAC) focuses on providing access based on user characteristics. Like rule-based access control, ABAC doesn’t involve employee roles and instead focuses on other factors, including location and group, to allow the system to grant access to employees.
Company owners can assign different types of attributes to employees, such as:
- Resource attributes: File names, file owners, and other digital characteristics
- Subject attributes: Department, group, security clearance level, and personal characteristics
- Action attributes: Characteristics involving how someone wants to act in order to access a resource
- Environmental attributes: External and contextual attributes such as visitor access time or company policies
Identity-based access control
Identity-based access control (IBAC) bases access control permission off of biometrics. Fingerprints and face structure are unique ways to give an individual access to areas within a business. Because face structure, fingerprints, and eye patterns are specific to each person, an IBAC system creates a simple way to control access without the chance of mistaken identity.
Smartphones, touchscreen systems, face scanners, touchpads, and more allow biometrics to form the basis for security at your business. Access control systems with video cameras and biometric detection give double assurance that customers will not have access to employee-only areas and that employees will have access solely to their assigned areas.
Choosing a Type of Access Control for Your Needs
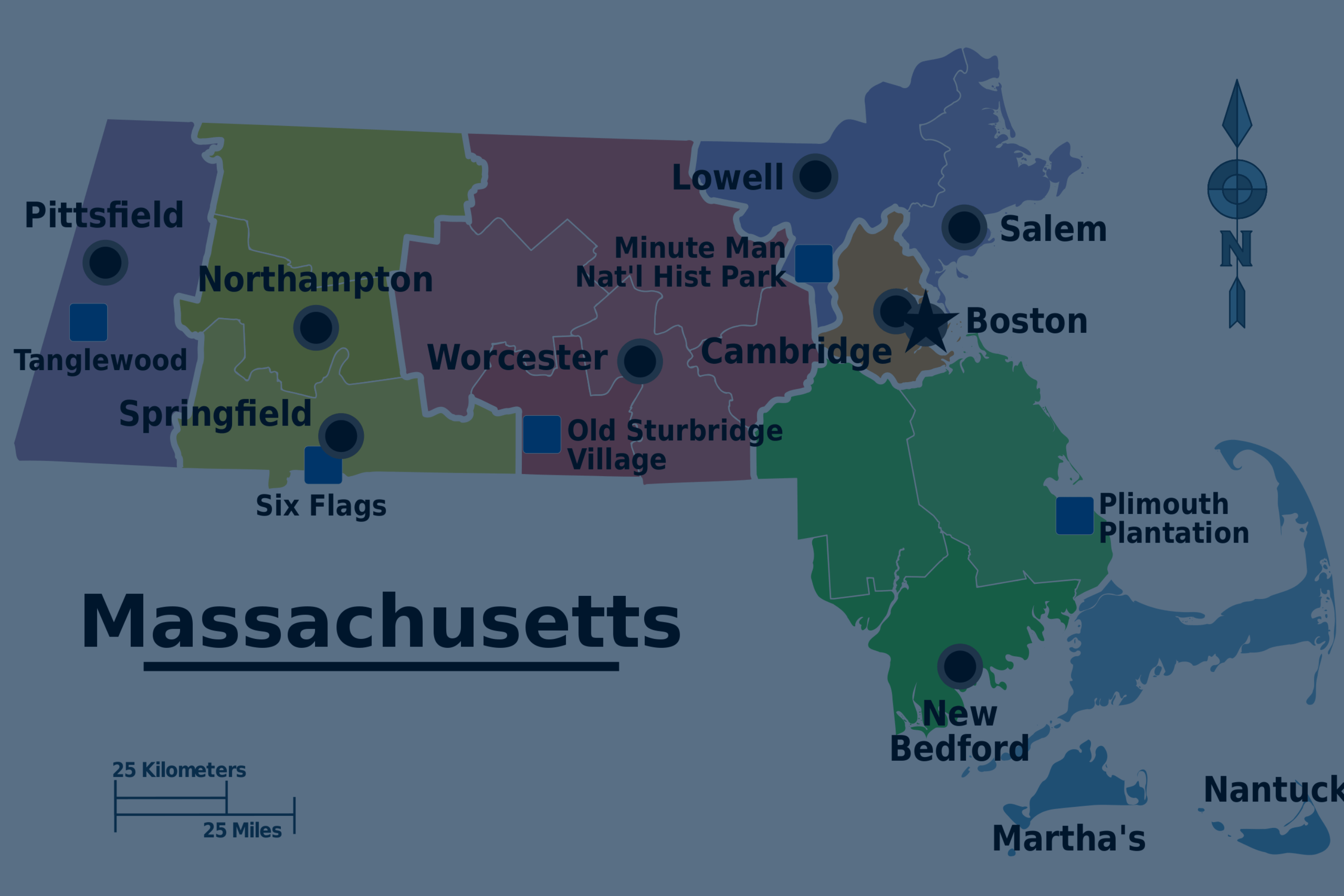
Whether you live in Massachusetts, Connecticut, or Rhode Island, Alarm New England can help you decide which type of access control is right for your security needs. Call a security specialist at 857-445-4010 to discuss your requirements for an access control system you can trust.